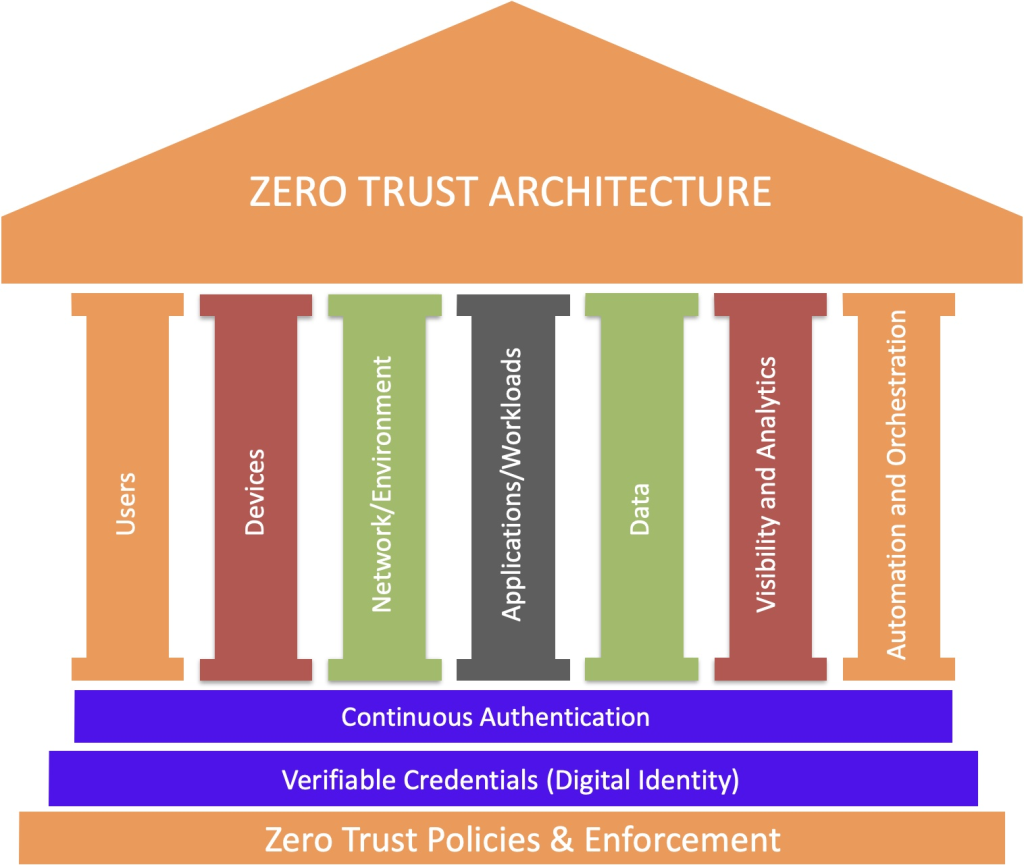
Cybersecurity is no longer just a back-office concern; it’s a top-line issue that shapes how organizations operate and protect what matters most: their people, data, and reputation. At the center of this evolving conversation is the Zero Trust model, based on the National Institute of Standards and Technology Special Publication 800-207 (NIST SP 8008-207), a security philosophy grounded in the principle of "never trust, always verify." While Zero Trust offers powerful tools to mitigate cyber threats, it’s not without its challenges. Overly rigid security postures can sometimes hinder productivity, create frustration, and even expose new vulnerabilities.
So, are companies striking the right balance? Are Chief Information Security Officers (CISOs) and Chief Information Officers (CIOs) focusing on the risks that matter most without stifling their teams or their businesses? Let’s unpack the promises and pitfalls of cybersecurity in the Zero Trust era.
Why Zero Trust Makes Sense
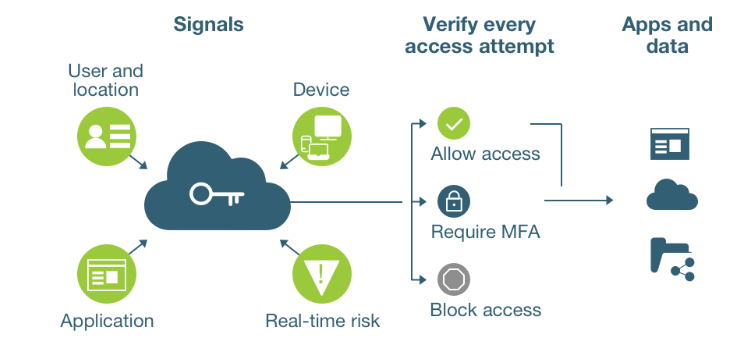
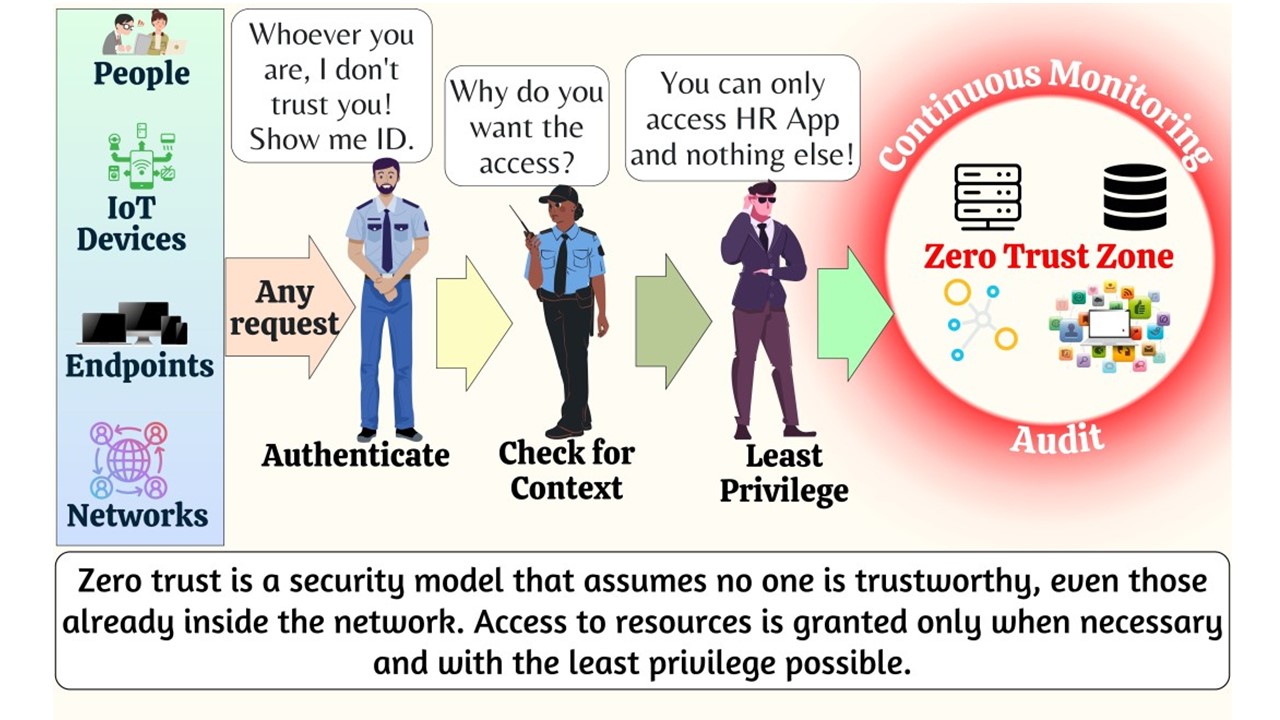
The push for stronger cybersecurity is undeniable. A single breach can cost millions, destroy trust, and cripple operations. Zero Trust helps prevent that by doing what older models didn’t: questioning everyone and everything. Trusting someone simply because they’re “inside” the network is no longer enough. Every device, user, and application must prove their legitimacy—every time.
This approach brings apparent benefits:
- Stronger Protection: Hackers can’t exploit what they can’t access. By minimizing trust, Zero Trust minimizes risk.
- Compliance Confidence: Many regulations now expect airtight controls, and Zero Trust helps meet those standards.
- Resilience: The model makes it harder for attackers to move freely within a system, even if they breach the first layer of defenses.
The Risks of Going Too Far
While Zero Trust is a game-changer, leaning too heavily on it can backfire. The irony is that, in trying to make systems airtight, we can unintentionally create new vulnerabilities or hurt the very people Zero Trust Models are trying to protect.
- Disrupting Workflows: When everything needs verification, tasks that used to take seconds might now take minutes—or longer. Over time, this friction adds up, leading to employee frustration and lost productivity.
- Ballooning Costs: Zero Trust isn’t cheap. It requires significant investments in technology, training, and maintenance, which can strain resources, especially for smaller businesses.
- Blind Spots Elsewhere: A hyper-focus on Zero Trust might overshadow other priorities, like educating employees or strengthening incident response plans. Cybersecurity isn’t just about prevention; it’s also about being prepared for when (not if) something goes wrong.
The Human Factor

One of the most overlooked aspects of cybersecurity is the human element. Security measures that are too complex or disruptive can push people to find workarounds—sharing passwords, bypassing protocols, or ignoring best practices. This behavior doesn’t come from malice but from a natural desire to make their work lives easier. Ironically, these shortcuts can introduce the risks Zero Trust aims to prevent.
Are CISOs and CIOs Getting It Right?

The challenge for CISOs and CIOs is deciding how much risk is acceptable. It’s a tough balancing act that must protect against the worst-case scenario without overreacting to every possible threat.
Some organizations fall into the trap of overpreparing for low-probability events while neglecting common vulnerabilities like phishing scams or weak passwords. Others might prioritize security so much that they unintentionally stifle creativity and collaboration, making their organization less agile and competitive.
The best leaders understand that cybersecurity isn’t about eliminating all risk—it’s about managing it thoughtfully. They focus on the most likely and impactful threats, communicate openly about trade-offs, and design systems that empower their teams instead of constraining them.
How to Strike the Right Balance

Achieving a balanced cybersecurity posture isn’t easy, but it’s possible with a thoughtful approach:
- Prioritize People: Design security measures that work for your teams, not against them. If employees feel supported rather than policed, they’re more likely to follow protocols.
- Focus on Likely Risks: Don’t get caught up in chasing every possible threat. Instead, allocate resources where they’ll make the biggest difference.
- Foster Collaboration: CISOs, CIOs, and business leaders must work together to align security with broader organizational goals. Cybersecurity should enable success, not hinder it.
- Adapt and Evolve: Cyber threats are constantly changing. Regularly review and adjust your strategies to stay ahead of the curve.
Zero Trust has rightfully earned its place as a cornerstone of modern cybersecurity, but it’s not a silver bullet. When implemented thoughtfully, it can protect against the threats of today and tomorrow. But when taken too far, it can create new challenges that leave organizations vulnerable in other ways.
CISOs and CIOs play a critical role in finding that balance. By managing risks pragmatically and keeping people at the center of their strategies, they can build a security posture that is both resilient and flexible—one that protects the organization without losing sight of its mission.
In the end, cybersecurity isn’t just about technology; it’s about trust—the trust employees have in their systems, the trust customers have in your organization, and the trust you have in your ability to respond to whatever comes next.